While Active and Passive attacks both belong to the family of security attacks there are few underlying points that differentiate them.
Before moving on to the differential factors let’s quickly get a brief understanding of each one of them.
What is an Active Attack?
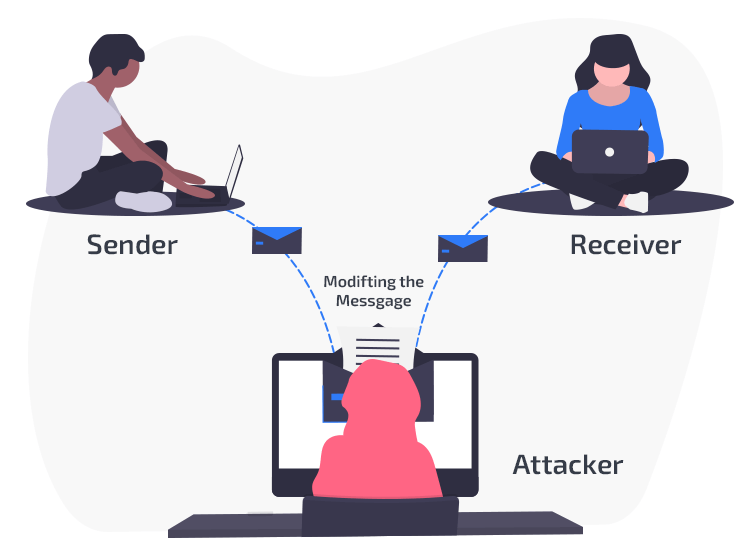
The modus operandi of an Active attack is to modify and alter the content to create a false statement. This poses a danger to the availability and integrity of the actual information. Interruption, modification, and fabrication are few forms of an Active attack.
- Interruption: Usually known as a masquerade attack, in there the attackers pose themselves as a legal entity to trick victims.
- Modification: This involves multiple series of replay and alterations. The original sequence of the data sent is captured and resend, it also involves alteration of the original message.
- Fabrication prevents the users from accessing certain services, It is normally termed as Denial of services where the hackers gain unauthorized access to the servers and block users’ access.
What is a Passive Attack?
In passive attacks, the attacker does not alter the information but observes and monitors it, copies it, and then uses it to interfere in the network traffics and attack targeted machines. Intruding and monitoring of information is the main motive behind a Passive attack.
In a passive attack the attacker looks out for open ports and network vulnerabilities and gains access to it as soon as it detects one.
The main differentiating points between an Active and Passive Attack
| Active Attack | Passive Attack |
| Work by modifying the information | No modification of information takes place. |
| It imposes a threat to the availability and integrity of the original piece of information. | It poses a danger to the confidentiality of the data. |
| There is a possibility of system damage. | No system damage. |
| Victims get informed about the attack | Victims are not informed about the attack. |
| In Active attacks, system resources can be altered and the main attention of the attack is on detection. | Here no alteration of system resources takes place and the main focus lies on prevention. |
How to prevent Active and Passive Attacks?
The best way to prevent a Passive attack is by using strong network encryption methods. This means that the original message should be well encrypted into an unintelligible language at the sender’s end and should be decoded into an understandable language at the receiver’s end. This also explains its major focus on prevention.
The use of powerful firewalls along with a strong intrusion prevention system can prevent and protect you from Active attacks.

