Every day new sophisticated forms of ransomware strains and variants are being developed and spread and one of them is Amber. Discovered by a malware analyst named Jakub Kroustek, Amber ransomware is a new variant of vicious file-encrypting Dharma ransomware.
This ransomware-type virus is created by cybercriminals with the sole intention to extract a huge sum of ransom money from innocent users. It operates by encrypting all types of user files (e.g., documents, images, audios, videos, etc.) stored on the computer and demands a ransom payment in the form of bitcoin cryptocurrency to decrypt them.
What is Amber Ransomware?
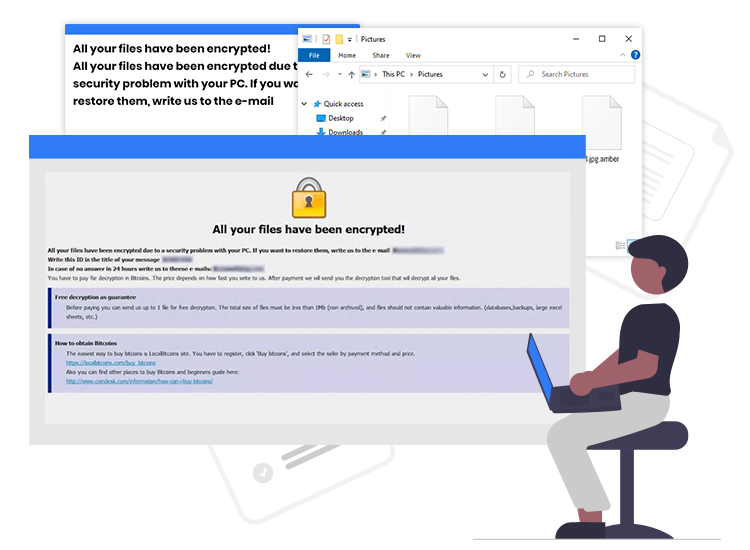
Amber ransomware is a notorious PC threat that encrypts user data using the strong AES-192 + RSA-2048 encryption algorithms. Similar to JoJoCrypt, VIPxxx, Ncovid, and several other ransomware-type infections, Amber changes the name of files during the encryption process.
It appends “[greenlite@keemail.me].amber” extension to the all affected filenames. For example, it renames a file named “1.mp3” to “1.mp3.[greenlite@keemail.me].amber”, “2.mp3” to “2.mp3.[greenlite@keemail.me].amber”, and so on.
After the encryption process is finished, it creates the “info.txt” text file (ransom note) and drops it into every folder containing the encrypted files. Typically, the text file created contains instructions on how to contact the attackers, price of decryption tool, pay a ransom, and so on.
Distribution Techniques
Cybercriminals can distribute ransomware and other malware infections through a variety of means. Below we have listed a few of the most common ones.
- Malicious email attachments, URLs, or ads
- Drive-by download
- Adult or porn-related websites
- Unofficial or freeware download sites
- Software flaws or bugs
How to Remove Amber Ransomware?
Downloading and installing a security software known for remediation and running a scan on the compromised system is the best way to deal with Amber ransomware and several other next-gen malware threats.
Important Tips on How to Prevent Ransomware Attacks
Follow the below-mentioned cybersecurity tips to avoid the fallout from ransomware attacks.
- Be sure your operating system and software are updated.
- Refrain yourself from downloading unexpected or suspicious email attachments.
- Back up your important files and folders using the 3-2-1 rule.
- Download files only from trusted and verified sites.
- Avoid connecting to free public Wi-Fi networks.

