An NTP Amplification attack belongs to the family of DDos attacks and is executed in large volumes. The attack takes place by exploiting the NTP- Network Time Protocol functionality to overburden a targeted network making it difficult for it to access the regular traffic.
In such kinds of attacks, the disparity between the bandwidth cost of the targeted server and attackers is exploited which results in a high disruption in the network infrastructure.
The high volume majorly comprises small multiple queries which result in large responses, this helps the attackers to avoid detection and also benefits them from the increase in traffic.
There is a vast difference between DNS Amplification attacks and DNS Flood attacks. In a DNS Amplification attack the origin of the attack is kept hidden by flooding the unsecured DNS servers with traffic, this also enhances the effectiveness of the attack. In addition to the smaller bandwidth connections are used to send thousands of requests to the targeted server, and while sending the response the attacker forges the return address.
Working Methodology of An NTP Amplification Attack
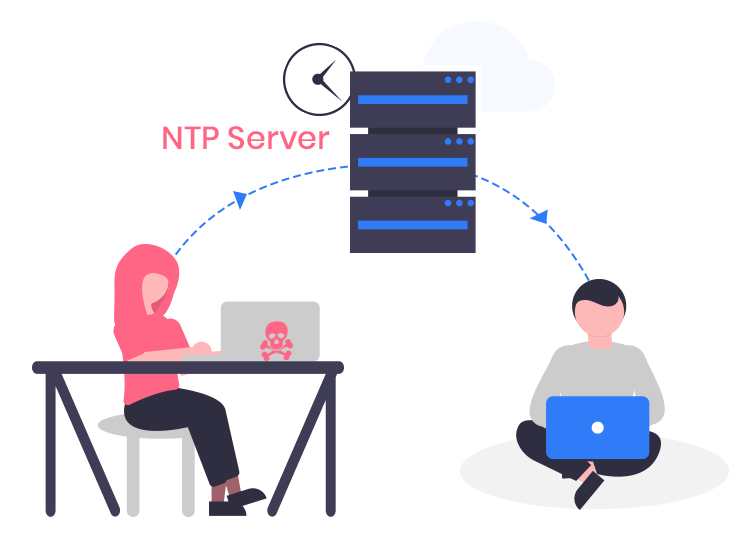
- UDP packets with spoofed IP are sent to NTP servers with the help of botnets. The fake IP addresses used here correspond to the real IP address of the victim.
- Monolist commands are used by each UDP packet to send requests to the targeted NTP server. This results in an amplified response.
- The server is then exploited to send responses to fake IP addresses.
- Once the IP address of the targeted server receives these responses, its network infrastructure gets flooded with traffic, resulting in a denial of service.
How To Mitigate NTP Amplification Attack?
The use of a powerful firewall mechanism is the first step towards fighting the NTP Amplification attack. In addition to this, the network capacity should also be increased to a sufficient limit.
Also, ensure that the operating system of your division is up-to-date with all the latest updates and thoroughly patched against all security loopholes.

